The Edge Layer
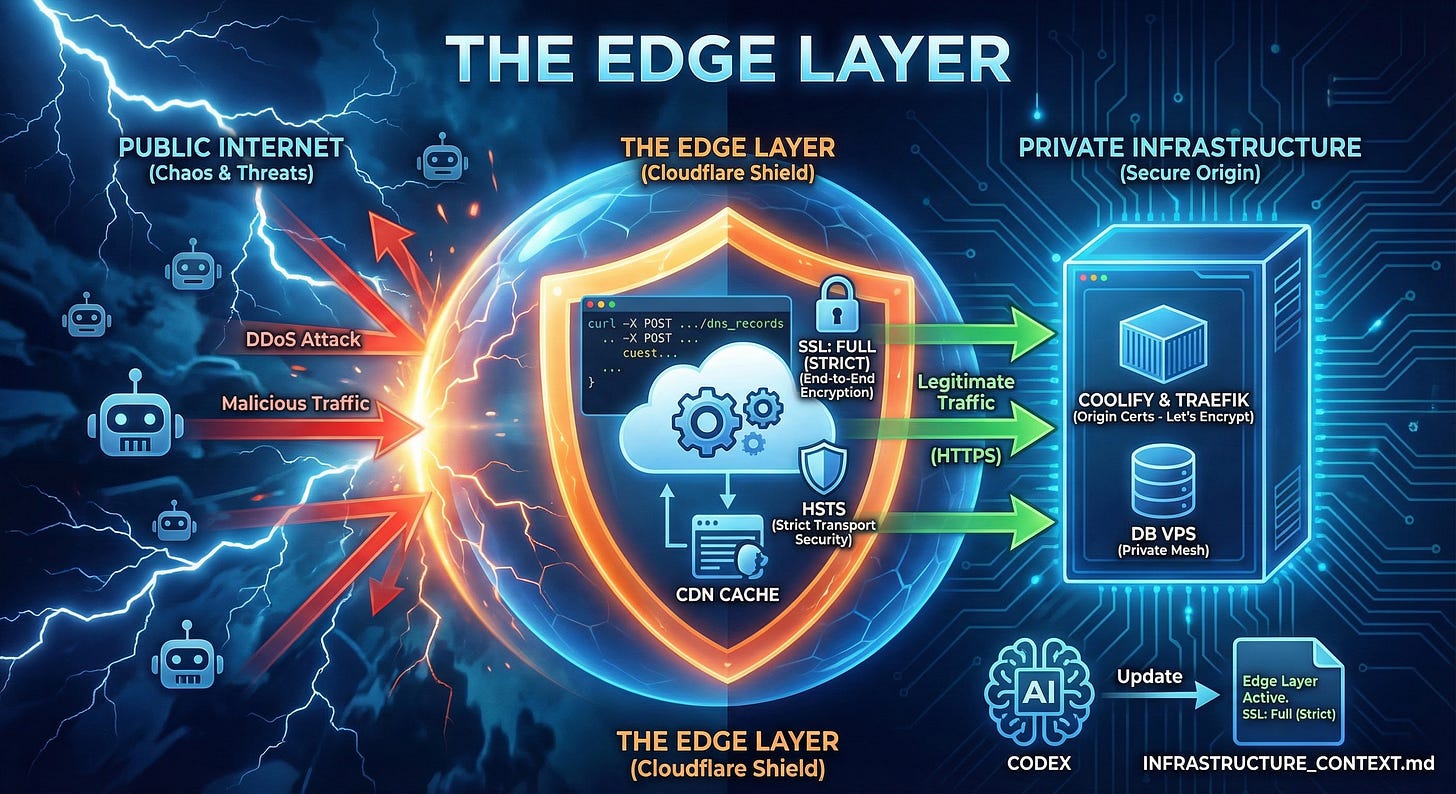
Objective: Configure Cloudflare as our global shield using curl and the Cloudflare API. We will implement “Full (Strict)” SSL, configure HSTS, and verify that Coolify’s internal Traefik proxy correctly handles certificate generation behind Cloudflare’s proxy.
1. The Edge Strategy
We are not exposing our server directly. We are putting Cloudflare in front.
DDoS Protection: Cloudflare absorbs attacks. Our IP is hidden.
Performance: CDN caches static assets at the edge.
SSL Offloading: Cloudflare handles the heavy crypto.
The Tool: Cloudflare API (via curl). We don’t click buttons in the UI. We write Infrastructure as Code using shell scripts.
2. DNS Configuration via API
We will manage our DNS records programmatically using the Cloudflare API. This allows us to version control our infrastructure.
Step 1: The Setup Script
Create a script setup_dns.sh locally. You will need your Zone ID and API Token.
Agent: Claude Code (Local) Prompt:
“Create a bash script setup_dns.sh to add Cloudflare DNS records using curl. Variables: ZONE_ID, TOKEN, IP=144.126.x.x, TAILSCALE_IP=100.x.y.z. Records to Create:
Root (@): A record to $IP, proxied (true).
Wildcard (*): CNAME to @, proxied (true).
Coolify (coolify): A record to $TAILSCALE_IP, proxied (false) - DNS Only.
The script should use: curl -X POST “https://api.cloudflare.com/client/v4/zones/$ZONE_ID/dns_records” ... “
Step 2: Execution
Run the script locally: export TOKEN=... ZONE_ID=...; bash setup_dns.sh
3. SSL Architecture: “Full (Strict)”
This is the most misunderstood setting.
Flexible: Encrypted to Cloudflare, Unencrypted to Server. BAD.
Full: Encrypted to Server, but accepts Self-Signed certs. OKAY.
Full (Strict): Encrypted to Server, requires Valid Trusted Cert. BEST.
We choose Full (Strict). This means our apps-vps MUST have a valid Let’s Encrypt certificate.
Traefik & Let’s Encrypt
Coolify uses Traefik. Traefik requests certs. The Magic: Cloudflare is smart enough to pass /.well-known/acme-challenge requests through to the origin, even when proxied.
4. Deployment Verification
Let’s prove it works.
Agent: Claude Code Prompt:
“Deploy a ‘Hello World’ Next.js app in Coolify. Domain: test.app.com. Verify:
curl -I https://test.app.com. Check for cf-cache-status.
Check SSL issuer: openssl s_client .... Should be Let’s Encrypt (on the backend) or Cloudflare (on the frontend).
Verify HTTP->HTTPS redirect.”
5. HSTS & Security Headers
HSTS (HTTP Strict Transport Security) tells browsers: “Never talk to me via HTTP again.” Enable this in Cloudflare Dashboard -> SSL/TLS -> Edge Certificates. Warning: Once enabled, you cannot downgrade to HTTP for months.
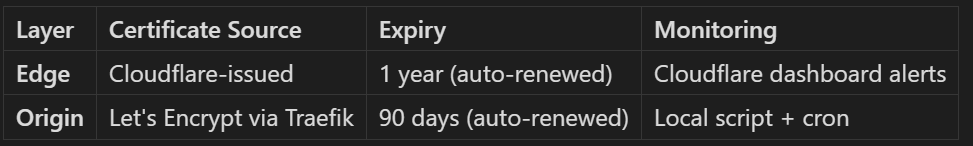
6. TLS Certificate Monitoring
You now have two layers of certificates to monitor:
Agent: Claude Code Prompt:
“We need to monitor both certificate layers.
Edge (Cloudflare): Use the TLS expiry script from Module 06 pointing at your public domain.
Origin (Traefik): Create check_coolify_origin_cert.sh to inspect Traefik’s cert files or connect directly to http://localhost:8000 (bypassing Cloudflare).
Add to cron alongside the edge check. Why both? Cloudflare can mask origin cert failures until you disable proxy mode.”
Reference: See 06. Observability Stack for the full monitoring script.
7. Context Update
Agent: Codex Prompt:
“Edge Layer Active. DNS: Managed via Cloudflare API scripts. SSL: Full (Strict). Security: Break-glass account created, 2FA active. Update INFRASTRUCTURE_CONTEXT.md.”
Next Step: The App Server is ready. Now for the heavy lifting. Go to 08. High-Performance Database.